[PDF] Nowadays, network topology design directly affects the security of the network. If the external and internal communications network, the internal network of the machine safety will be threatened, but also on the same network affect many other systems. Spread through the network, but also affect connected to the Internet / Intranet other network; As a result, may also involve legal, financial and other security-sensitive areas. Therefore, we design it is necessary to open the server and external network and internal network of other services necessary isolation, to avoid network structure information leakage; while also external network service requests are filtered, only allows normal communication of data packets reach the appropriate host, the other hosts request service before reaching it should be rejected.
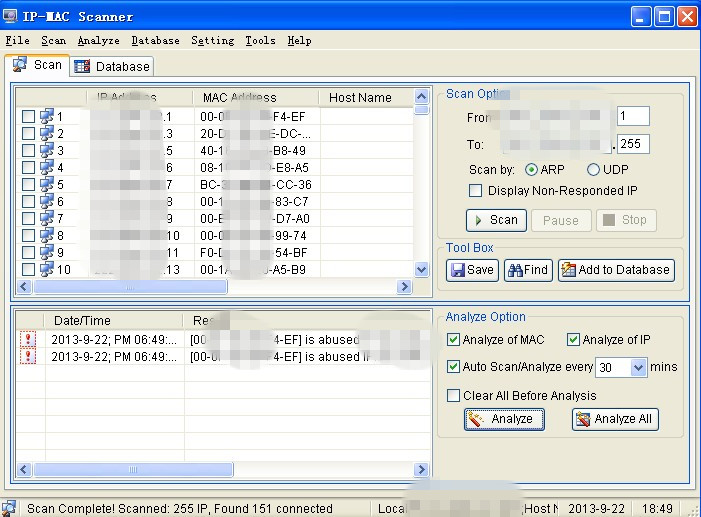
Therefore, we should add the trusted PCs into our database, for one thing, it can be more safer; for another thing, it can be convenient compared with other softwares. As in this case, i will introduce you a actual case that is to backup your trusted clients. Firstly, please open our IP-MAC Scanner software and then click the button “Scan”, and then you will get a list of computers in your local area network, as in the range of “*.*.*.1-*.*.*.255”. In my LAN, there are 151 PCs connected, which is be seen in the first picture.
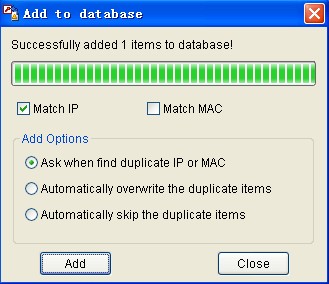
If you trust one connected PC, you can add it to the database and then get the response from out software, which is displayed in the following picture.
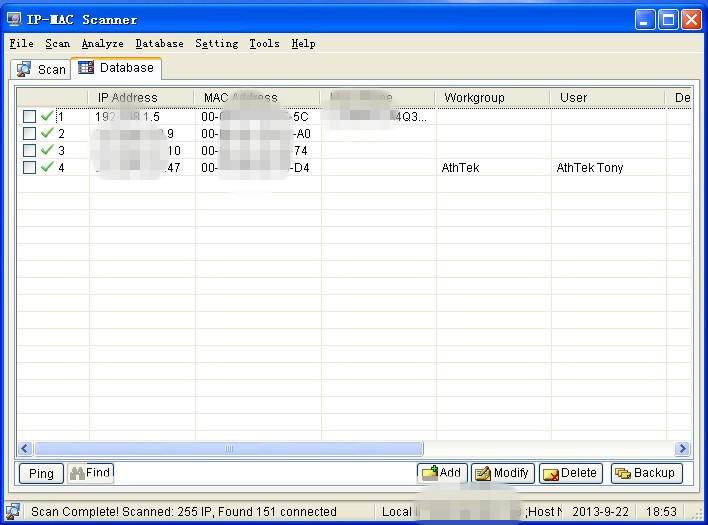
Finally, you will see the trusted one in your database, such as in the last picture, and you can modify its work-group and user as the following actual case, for instance, Workgroup: AthTek and User: AthTek Tony.
MORE DETAILS: http://www.athtek.com/blog/